Setting up a CAS Server
Background
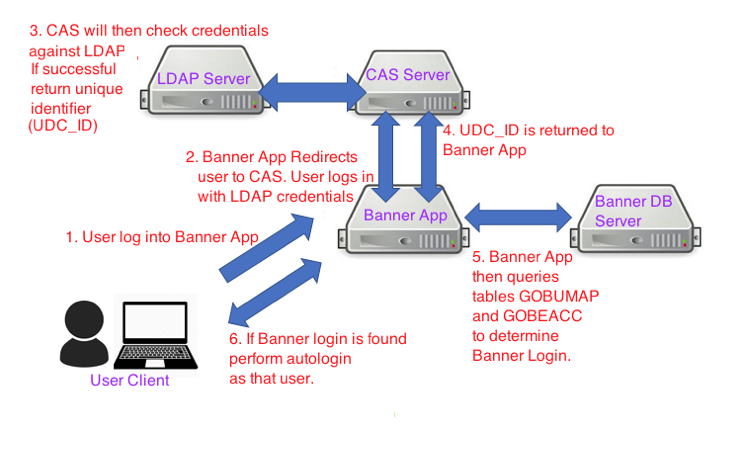
The Central Authentication Server (CAS) is used by Ellucian Banner to perform Single-Sign-On authentication services for Banner 9/INB and SSB products. CAS functions in the following manner:
- It will validate a username and password against an LDAP server.
- If successful, it will then query that user entry to return a unique identifier associated with that username.
- This identifier is then checked against internal Banner Tables (GOBEACC and GOBUMAP) to determine the associated internal Banner username.
- If the internal Banner username is found, it will then attempt to authenticate using that value.
The overall process flow for a Banner Application CAS login can be summarized as follows:
Setting up and Configuring CAS
- Download: CAS is a tomcat application. It can be installed on any Tomcat 7 or 8 application server. The package can be downloaded from https://www.apereo.org/projects/cas. However, please note that various spring configuration plugins are not included in the default install and must be added manually.
- Nyquest Consulting, LLC provides a copy of the CAS server code with all dependencies, which is available on request. Contact Us for more information
- Install: Once all dependencies are resolved, repack the CAS directory (jar -cf cas.war cas) and then copy it into the /webapps directory of any standard Tomcat installation.
- SSL Configuration: CAS requires SSL. Since it is an authentication app, CAS will not work unless Tomcat is configured with at least one SSL connector. You will need to purchase an SSL Certificate if you have not already done so. Sample configuration files for setting up SSL under both tomcat 7 and 8 are available at: /showpage/settingup-tomcat-ssl
The connector can be either from Tomcat directly or from using apache-httpd. Please note the SSL certificate must be added into the Java truststore which is running tomcat.
(See: https://docs.oracle.com/cd/E19830-01/819-4712/ablqw/index.html)
- LDAP Server configuration/setup: Prior to installing CAS, be sure to have the following information about your LDAP server:
- LDAP hostname
- LDAP Server Port
- LDAP Context
You must have an LDAP server for CAS to authenticate against. In most cases, this will be from Active Directory. However, for sites that do not have Microsoft, OpenLDAP seems to work also.
In addition, you must also create an LDAP user that has the ability to browse the entire LDAP tree. This is required so that attributes can be looked up when a user authenticates.
Finally, each user under LDAP MUST have at least ONE attribute that is unique. The attribute name can be anything as long as the value is unique for all accounts (example EmployeeNumber). This attribute will be returned by CAS if they successfully authenticate.
- If LDAP is running with SSL, the SSL certificate must also be added into the Java truststore which is running tomcat (see step #3).
- CAS Setup: The main configuration file for CAS is the deployerConfigContext.xml located under the WEB-INF directory. The hostname of the LDAP server, LDAP context and LDAP. This specific of the file will be discussed in the next section.
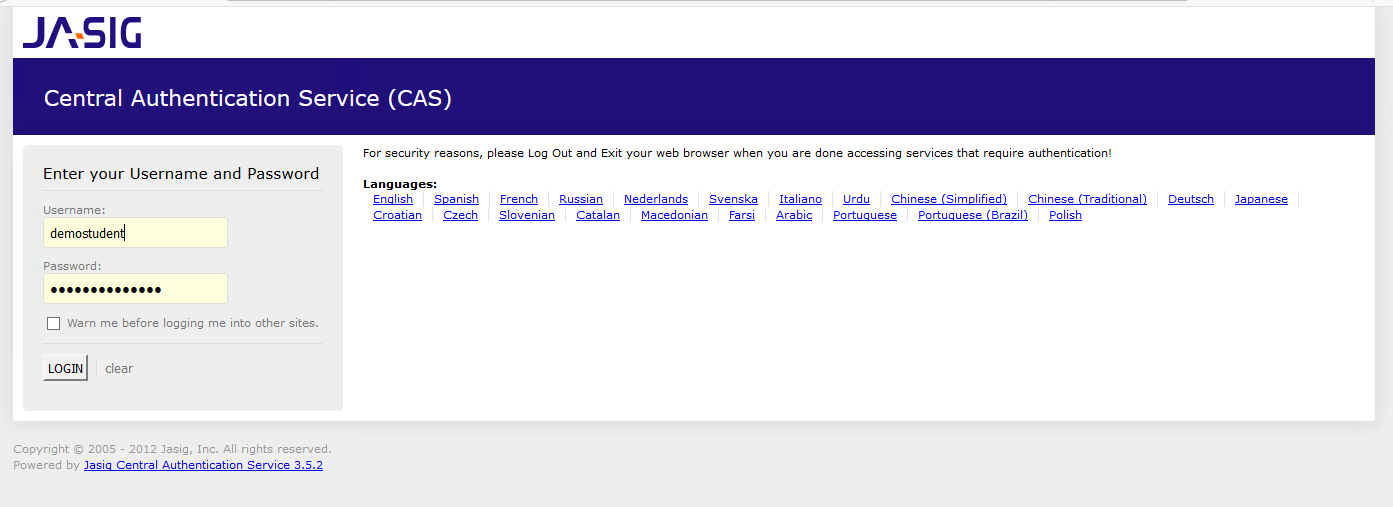
- Once CAS is configured you should be able access the main login screen as shown below at https://[tomcat server hostname]:[port]/cas/login
- After a successful authentication, a CAS ticket will be written to your browser. You will now be able to access ANY (CASIFIED) application that is configured to accept this ticket,
- The CAS logout URL: https://[tomcat server hostname]:[port]/cas/logout will expire any active ticket. Use this when you wish to exit your application.
Setting up deployerConfigContext.xml
Several changes need to be made in this file. Simply search for the various code blocks.
| Parameter |
|
| LDAP Server and Port |
<bean id="LDAPcontextSource" class="org.springframework.ldap.core.support.LdapContextSource">
<property name="pooled" value="false"/> <property name="urls"> <list> <value>ldap://my.ldaphost:port</value> </list> </property> |
|
LDAP User Password and Base Domain
1. Specify the username and password for your LDAP user here. You must also specify the context of this user. Remember the user must have FULL abilities to browse the LDAP Tree Note the username/password and context must be entered in (2) places. 2. You must also specify the BASE DN of the LDAP Tree |
<property name="userDn" value="CN=username,ou=context,dc=context,dc=more-context " />
<property name="password" value="password for username" /> <property name="baseEnvironmentProperties"> <map> <entry> <key> <value>java.naming.security.authentication</value> </key> <value>simple</value> </entry> </map> </property> </bean> <sec:user-service id="userDetailsService"> <sec:user name="username" password="password for username" authorities="ROLE_ADMIN" /> </sec:user-service> |
|
Unique Attribute UDC_IDENTIFIER
In this example the EmployeeNumber will be returned. This value will then passed into Banner and checked against GOBEACC and GOBUMAP. |
<property name="resultAttributeMapping"> <map> <entry key="employeeNumber" value="UDC_IDENTIFIER" /> <entry key="sAMAccountName" value="uid" /> </map> </property> |
Setting up the Banner Mapping Tables (GOBUMAP and GOBEACC)
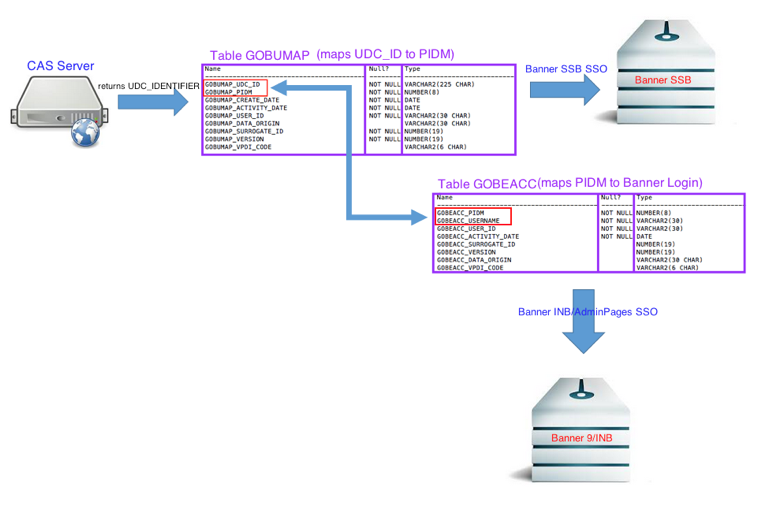
If the authentication to CAS is successful, a unique identifier (UDC_IDENTIFIER) will be return from CAS to the Banner application.
Banner will then check following tables
- GOBUMAP: this table contains the mapping for UDC_IDENTIFIER TO PIDM. It is used for Banner Self Service authentication
- GOBEACC: this table contains a mapping for PIDM to Banner INB/9 login username. It is used for Banner Admin pages/INB login.
Users that want to login to Banner SSB using CAS must have a record in GOBUMAP.
Users that want to login to Banner 9/INB using CAS must have a record in BOTH GOBUMAP and GOBEACC.
Setup of CAS with Ellucian Banner Applications
After CAS is setup, you will need to enter this information into the various Banner applications:
Banner 8 INB and SSB require SSOManager. In most cases you will need to rebuild SSOManager with the updated CAS server information. The CAS server URL can be validated in the SSOManager application, but cannot be changed.
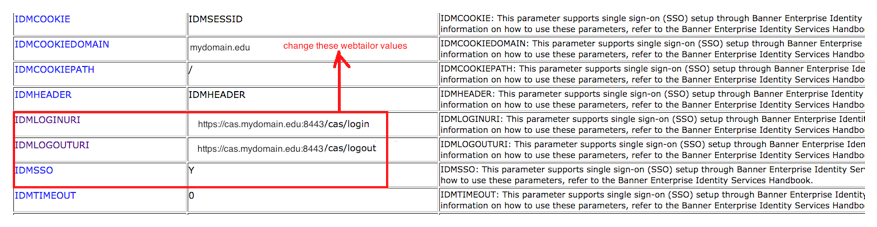
In addition, if you are running Banner 8 SSB, you must update the Webtailor values IDMLOGINURI, IDMLOGOUTURI, and IDMSSO to your CAS login URL, logout URL, and Y, respectively.
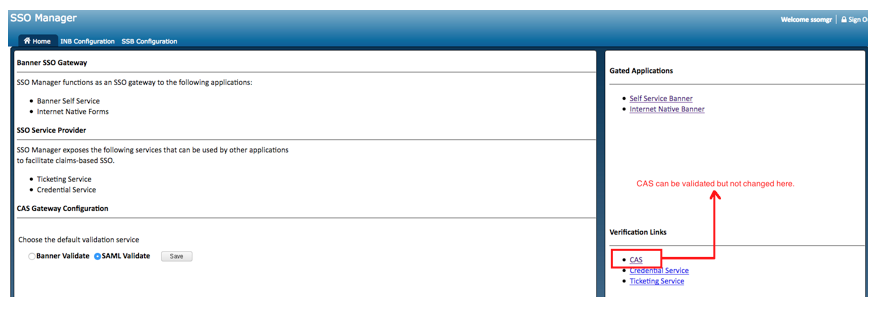
Navigate to: Webtailor Administration->Webtailor Parameters as shown below:
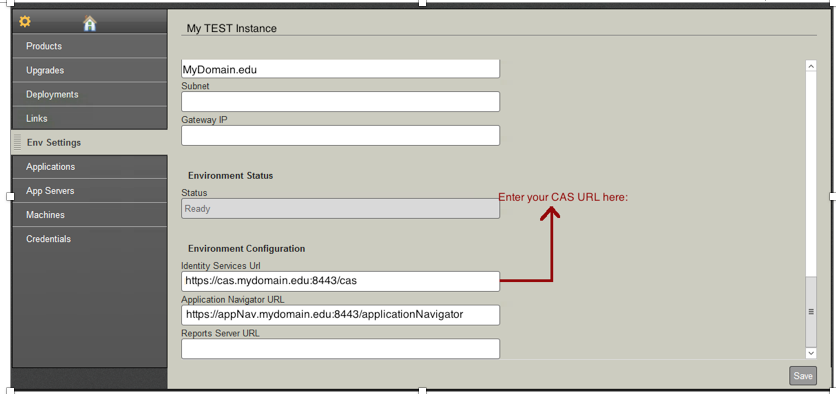
Finally, if you are running Banner 9, you must update the CAS server URL for the corresponding Banner instance under Ellucian Solution Manager (ESM)